提问之前请先在 1Panel 问题排查思路 找一下有没有解决方案
提需求请在 GitHub · Where software is built 这里提 100% 回复
应用安装失败 请参考 Docker Hub 无法访问:应用安装失败,镜像拉取超时的解决方案
反馈问题【BUG】请附带以下信息
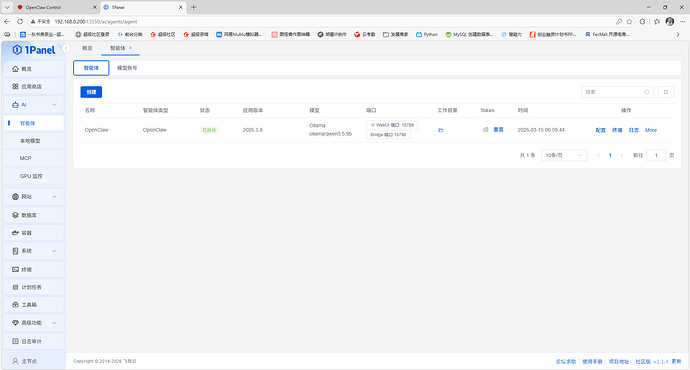
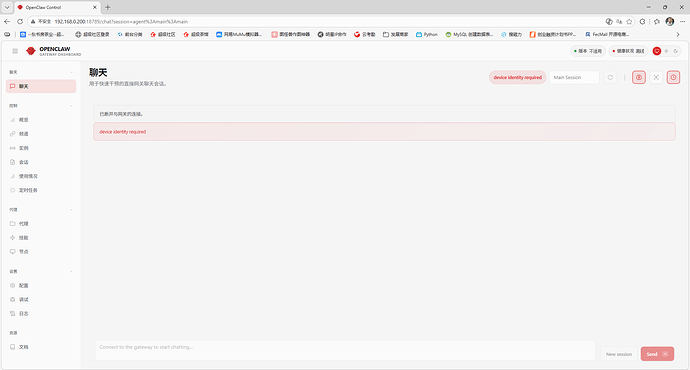
1Panel 版本:v2.1.4
操作系统(设备): Ubuntu 24.04.4 LTS
关键截图:
日志:1Panel-openclaw-wOao | 2026-03-16T13:19:55.333+00:00 [gateway] ![]() Gateway is binding to a non-loopback address. Ensure authentication is configured before exposing to public networks.
Gateway is binding to a non-loopback address. Ensure authentication is configured before exposing to public networks.
1Panel-openclaw-wOao | 2026-03-16T13:19:55.334+00:00 [gateway] ![]() gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback=true is enabled. Host-header origin fallback weakens origin checks and should only be used as break-glass.
gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback=true is enabled. Host-header origin fallback weakens origin checks and should only be used as break-glass.
1Panel-openclaw-wOao | 2026-03-16T13:19:55.381+00:00 [heartbeat] started
1Panel-openclaw-wOao | 2026-03-16T13:19:55.387+00:00 [health-monitor] started (interval: 300s, startup-grace: 60s, channel-connect-grace: 120s)
1Panel-openclaw-wOao | 2026-03-16T13:19:55.390+00:00 [gateway] agent model: ollama/qwen3.5:9b
1Panel-openclaw-wOao | 2026-03-16T13:19:55.392+00:00 [gateway] listening on ws://0.0.0.0:18789 (PID 7)
1Panel-openclaw-wOao | 2026-03-16T13:19:55.394+00:00 [gateway] log file: /tmp/openclaw/openclaw-2026-03-16.log
1Panel-openclaw-wOao | 2026-03-16T13:19:55.395+00:00 [gateway] security warning: dangerous config flags enabled: gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback=true, gateway.controlUi.dangerouslyDisableDeviceAuth=true. Run openclaw security audit.
1Panel-openclaw-wOao | 2026-03-16T13:19:55.420+00:00 [browser/server] Browser control listening on http://127.0.0.1:18791/ (auth=token)
1Panel-openclaw-wOao | 2026-03-16T13:19:56.428+00:00 [gateway] signal SIGTERM received
1Panel-openclaw-wOao | 2026-03-16T13:19:56.429+00:00 [gateway] received SIGTERM; shutting down
1Panel-openclaw-wOao | 2026-03-16T13:19:56.441+00:00 [gmail-watcher] gmail watcher stopped
1Panel-openclaw-wOao | (node:7) [DEP0040] DeprecationWarning: The punycode module is deprecated. Please use a userland alternative instead.
1Panel-openclaw-wOao | (Use node --trace-deprecation ... to show where the warning was created)
1Panel-openclaw-wOao | 2026-03-16T13:19:59.502+00:00 [canvas] host mounted at http://0.0.0.0:18789/__openclaw__/canvas/ (root /home/node/.openclaw/canvas)
1Panel-openclaw-wOao | 2026-03-16T13:19:59.504+00:00 [gateway] ![]() Gateway is binding to a non-loopback address. Ensure authentication is configured before exposing to public networks.
Gateway is binding to a non-loopback address. Ensure authentication is configured before exposing to public networks.
1Panel-openclaw-wOao | 2026-03-16T13:19:59.505+00:00 [gateway] ![]() gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback=true is enabled. Host-header origin fallback weakens origin checks and should only be used as break-glass.
gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback=true is enabled. Host-header origin fallback weakens origin checks and should only be used as break-glass.
1Panel-openclaw-wOao | 2026-03-16T13:19:59.553+00:00 [heartbeat] started
1Panel-openclaw-wOao | 2026-03-16T13:19:59.559+00:00 [health-monitor] started (interval: 300s, startup-grace: 60s, channel-connect-grace: 120s)
1Panel-openclaw-wOao | 2026-03-16T13:19:59.562+00:00 [gateway] agent model: ollama/qwen3.5:9b
1Panel-openclaw-wOao | 2026-03-16T13:19:59.564+00:00 [gateway] listening on ws://0.0.0.0:18789 (PID 7)
1Panel-openclaw-wOao | 2026-03-16T13:19:59.566+00:00 [gateway] log file: /tmp/openclaw/openclaw-2026-03-16.log
1Panel-openclaw-wOao | 2026-03-16T13:19:59.567+00:00 [gateway] security warning: dangerous config flags enabled: gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback=true, gateway.controlUi.dangerouslyDisableDeviceAuth=true. Run openclaw security audit.
1Panel-openclaw-wOao | 2026-03-16T13:19:59.592+00:00 [browser/server] Browser control listening on http://127.0.0.1:18791/ (auth=token)
1Panel-openclaw-wOao | 2026-03-16T13:20:02.595+00:00 [ws] security warning: websocket origin accepted via Host-header fallback conn=c659e7b4-90fe-4bcc-8bc8-d522352361ca count=1 host=192.168.0.200:18789 origin=http://192.168.0.200:18789
1Panel-openclaw-wOao | 2026-03-16T13:20:02.597+00:00 [gateway] security metric: gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback accepted a websocket connect request
1Panel-openclaw-wOao | 2026-03-16T13:20:02.606+00:00 [ws] closed before connect conn=c659e7b4-90fe-4bcc-8bc8-d522352361ca remote=192.168.0.222 fwd=n/a origin=http://192.168.0.200:18789 host=192.168.0.200:18789 ua=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/146.0.0.0 Safari/537.36 Edg/146.0.0.0 code=4008 reason=connect failed
1Panel-openclaw-wOao | 2026-03-16T13:20:18.597+00:00 [ws] security warning: websocket origin accepted via Host-header fallback conn=9fd0873a-7478-4109-979a-5b7cf308c77e count=2 host=192.168.0.200:18789 origin=http://192.168.0.200:18789
1Panel-openclaw-wOao | 2026-03-16T13:20:18.599+00:00 [gateway] security metric: gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback accepted a websocket connect request
1Panel-openclaw-wOao | 2026-03-16T13:20:18.603+00:00 [ws] closed before connect conn=9fd0873a-7478-4109-979a-5b7cf308c77e remote=192.168.0.222 fwd=n/a origin=http://192.168.0.200:18789 host=192.168.0.200:18789 ua=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/146.0.0.0 Safari/537.36 Edg/146.0.0.0 code=4008 reason=connect failed
1Panel-openclaw-wOao | 2026-03-16T13:20:34.589+00:00 [ws] security warning: websocket origin accepted via Host-header fallback conn=6fbae6f3-09b8-4d14-80c1-a5ee912ce51a count=3 host=192.168.0.200:18789 origin=http://192.168.0.200:18789
1Panel-openclaw-wOao | 2026-03-16T13:20:34.593+00:00 [gateway] security metric: gateway.controlUi.dangerouslyAllowHostHeaderOriginFallback accepted a websocket connect request
1Panel-openclaw-wOao | 2026-03-16T13:20:34.600+00:00 [ws] closed before connect conn=6fbae6f3-09b8-4d14-80c1-a5ee912ce51a remote=192.168.0.222 fwd=n/a origin=http://192.168.0.200:18789 host=192.168.0.200:18789 ua=Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/146.0.0.0 Safari/537.36 Edg/146.0.0.0 code=1008 reason=device identity required
没有上述信息的问题很有可能不被回答